A Collection edge — Kavach at the forefront
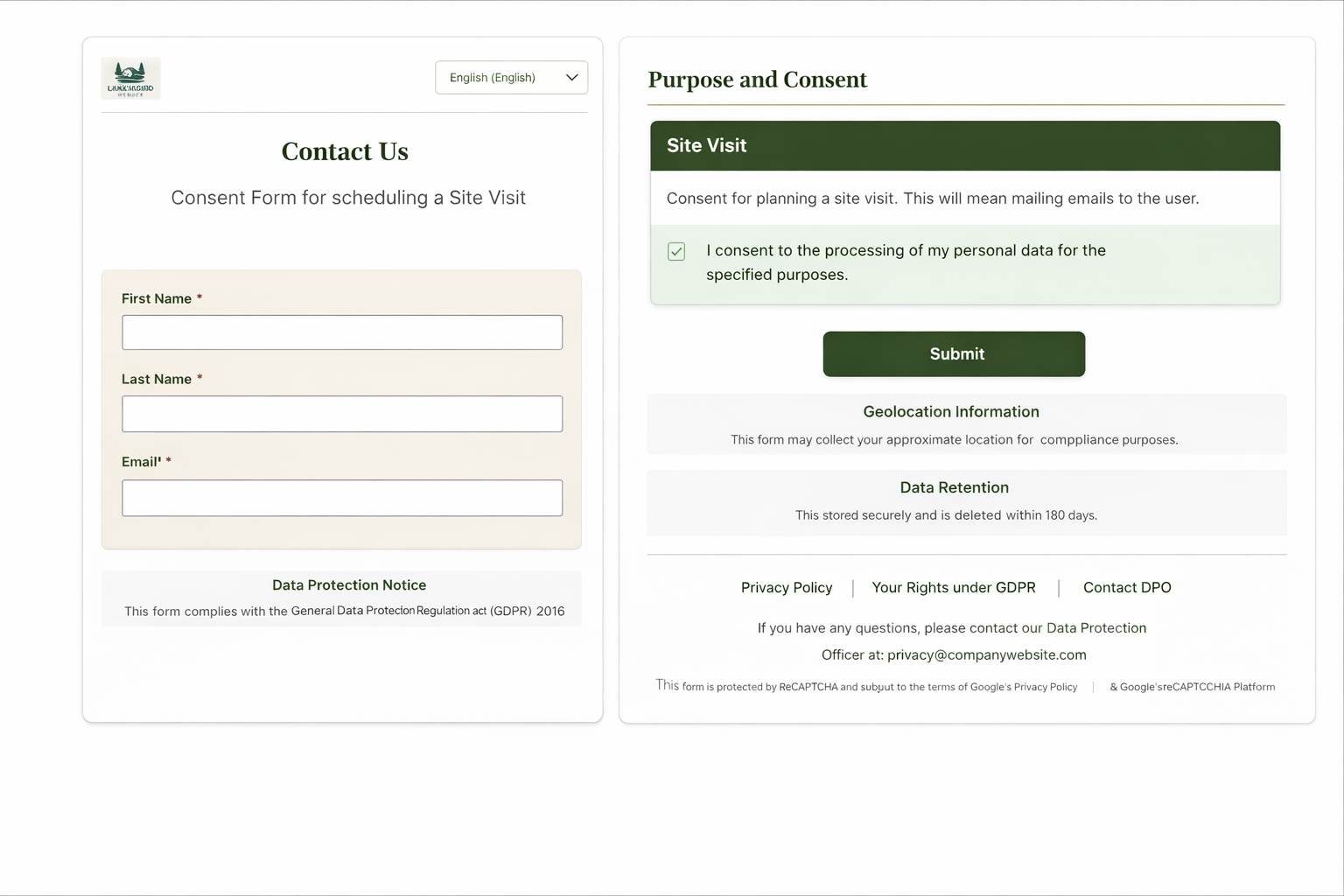
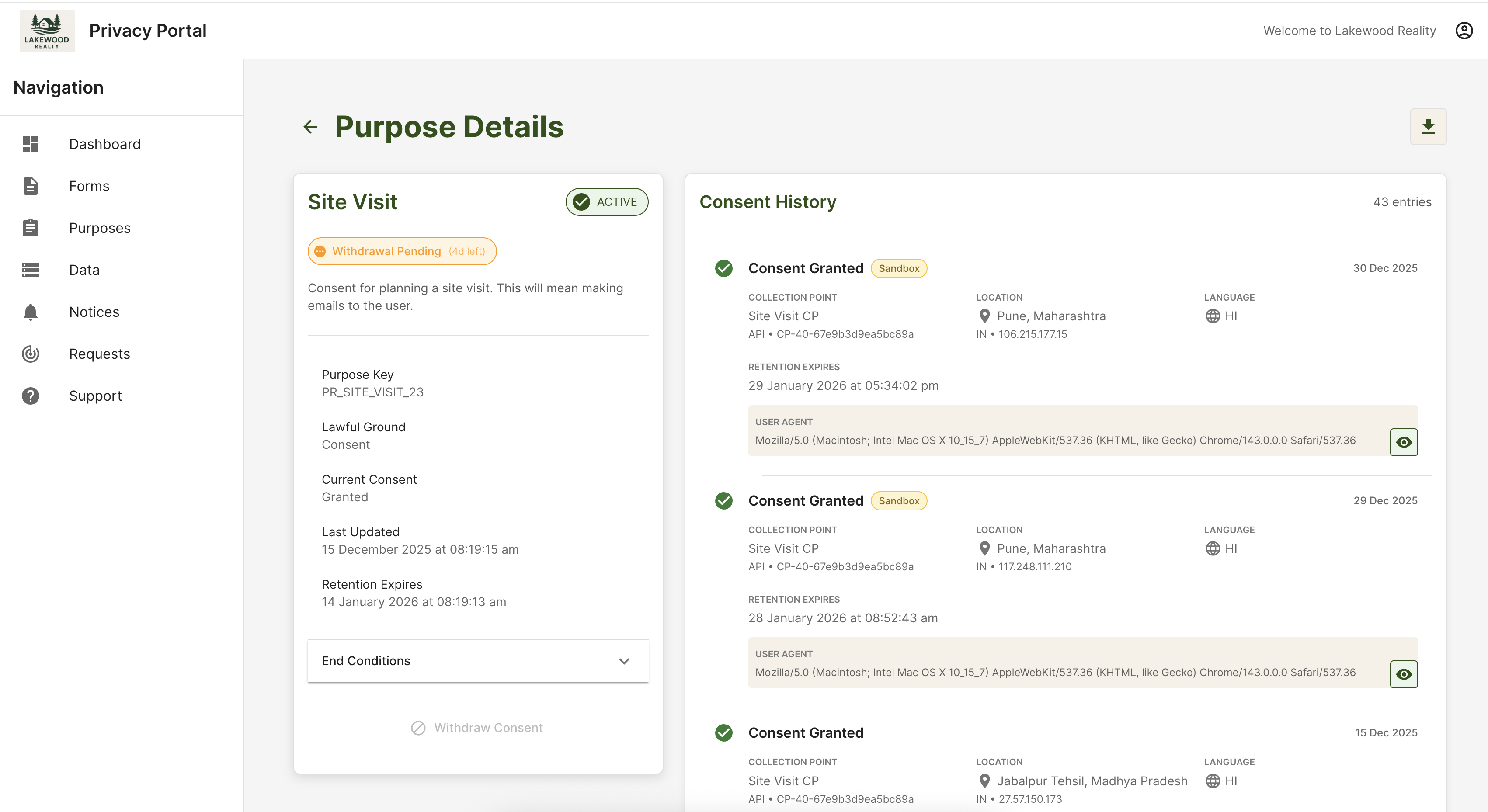
Principals interact with Kavach-rendered notices and purpose controls at the moment personal data is collected: hosted forms, embeds, and collection points wired to your domains.
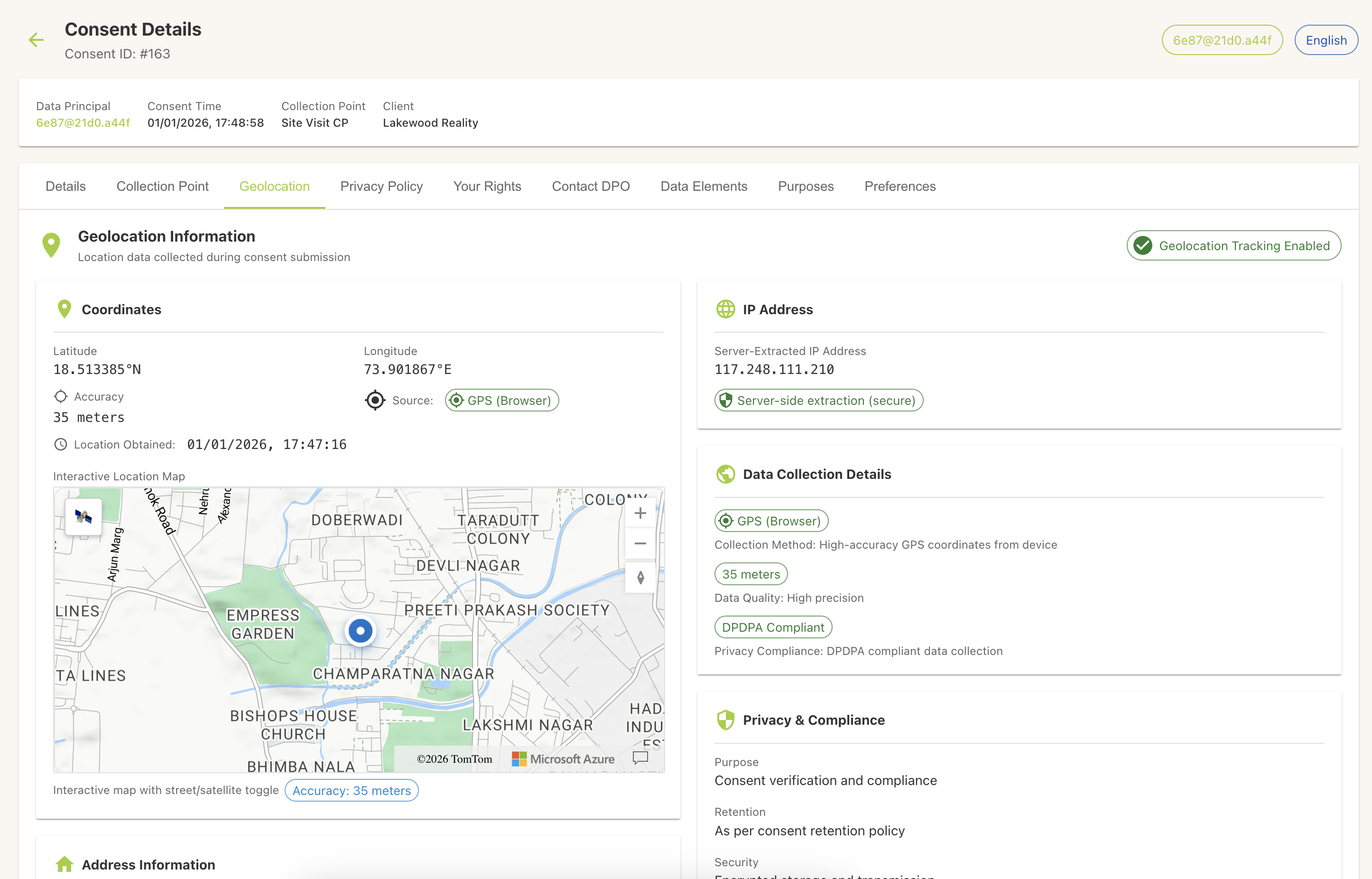
- Notice and purpose text is versioned and bound to the submission payload before any downstream persistence.
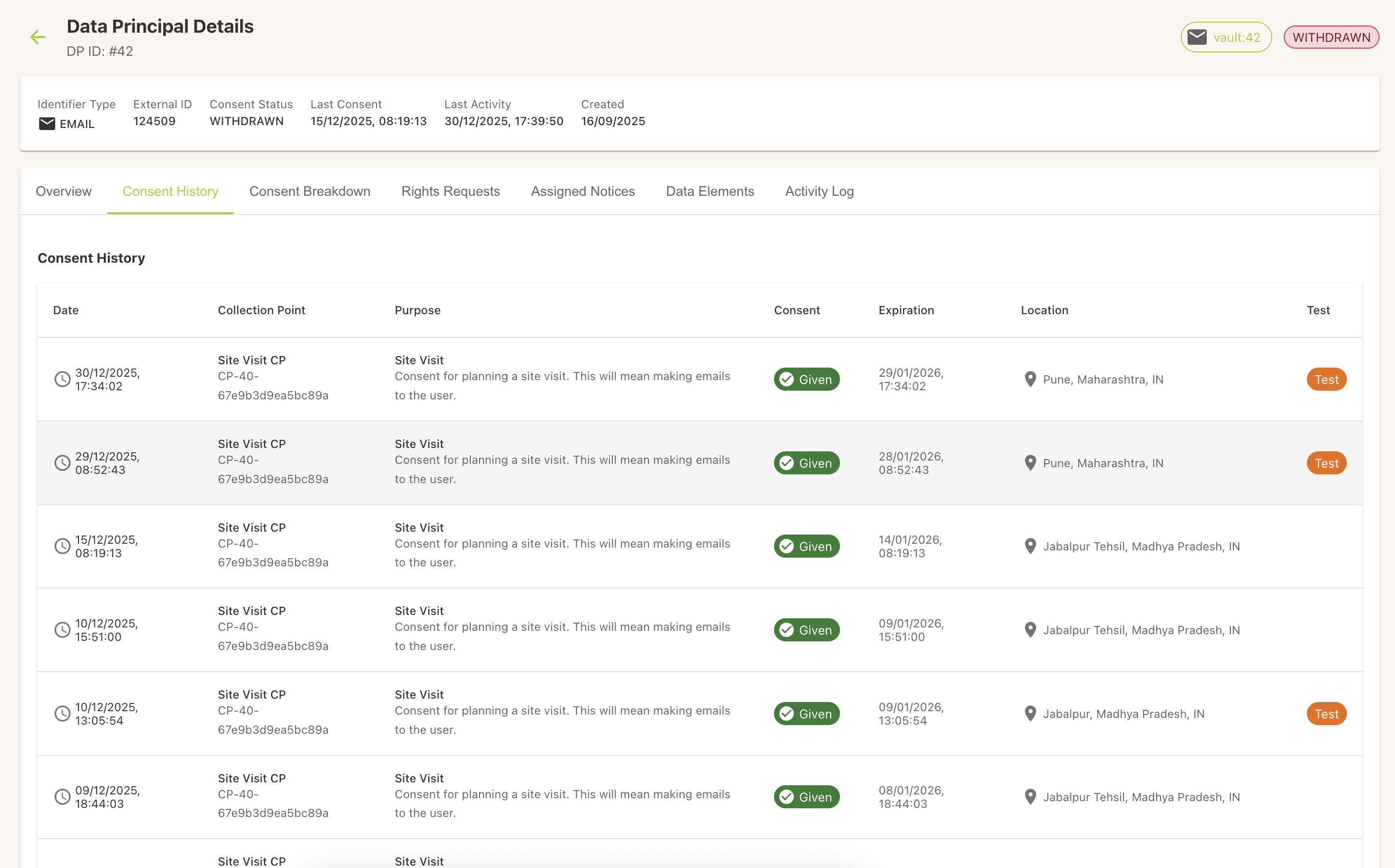
- Consent events land in the vault-backed ledger first; webhooks and API callbacks notify CRM, onboarding, or fulfilment systems to proceed with a correlation ID and purpose map.
- Ideal when you need maximum defensibility at the capture surface or multi-language notices without redeploying legacy apps.